Investigations revealing indicators missed prior to a crime are all too common. Learn how the right software solution can prevent this from happening.
“Did we miss the clues that could have identified this plot and its players before the attack?”
“Why weren’t the dots connected?”
“Could something have been done to prevent this incident?”
After a mass shooting or a terrorist attack and during the post-mortem of the incidents, questions like these are asked as people scramble to make sense of such a tragedy.
In some of these cases, the investigations reveal that there were indicators or information that was in fact missed or not connected. Sometimes the dots were not connected due to a lack of ability to share information among law enforcement agencies in various levels of government. In other instances, signs may have been missed because a manual analysis of the data failed to link the information.
Whatever the reason, having the right tools to help can mean the difference between solving a crime and leaving the dots unconnected.
Connecting the Dots
Whether it’s a lack of information or human error, establishing Regional Information Sharing Systems (RISS) and Fusion Centers may be part of the answer. But, even with these law enforcement resources up and running, there are still incidents that are falling through the cracks. In addition, these assets’ ability to help connect the dots, are only as good as the information they are given.
So, what more can we do? One suggestion to assist with trying to fill some of the cracks at an agency or department level is to look beyond your agency’s Records Management System (RMS) and incorporate investigation management software. The right investigation management software has powerful algorithms for criminal pattern identification and link analysis that can aid local law enforcement agencies with this issue among others.
For example, several officers from the same agency may be from different commands, precincts, districts, or station houses. While they’re all a part of the same agency, they’re situated remotely from one another and taking Suspicious Activity Reports (SARs) – likely in a vacuum.
While their individual reports are associated with possible terrorist activities, those activities may be happening days apart – and being filed across precincts without each other’s knowledge. It may turn out that all incidents are related.
The officers follow their departments’ protocols and file the SARs for analysis and distribution to the appropriate entities. If an agency has investigation management software, after the SARs have been uploaded, a simple search of any information in the SARs (like names, addresses, vehicle descriptions or license plate numbers) may reveal the link of all these SARs.
And, if there is an open case which involves any of the information contained in the SARs, the case investigator can get an immediate notification of this information, once the SARs have been entered into the system.
Here’s an example of a link analysis for the fictitious scenario discussed above, utilizing the search of an address involved in the SARs:
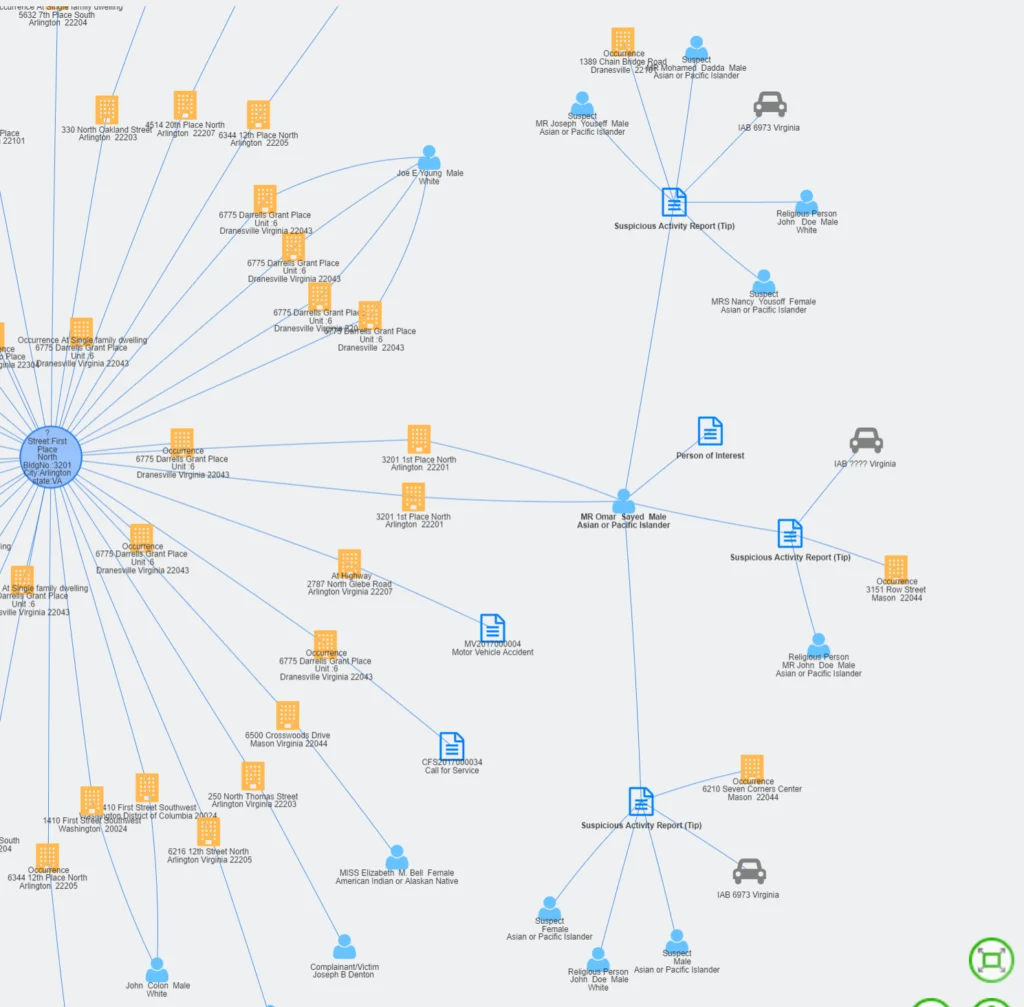
Figure A: SARs linked by address search
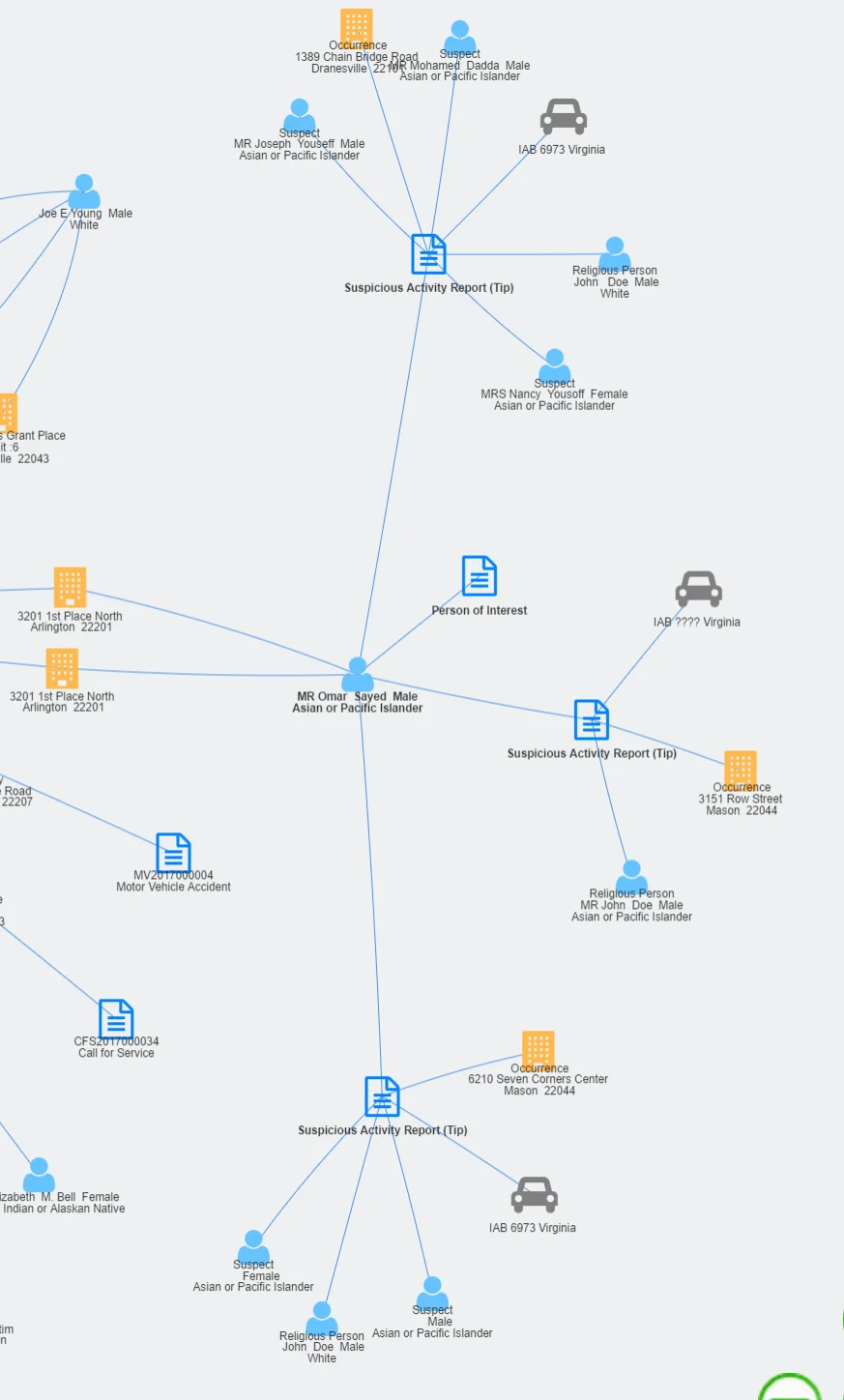
Figure B: Closeup of link analysis from SARs, linking names, vehicles and locations, from all the data on the searched address
In addition to a SAR link analysis, this type of software can:
- See calls for service (9-1-1)
- Read criminal reports
- Discover motor vehicle accident reports
- See calls for medical assistance
- Look at photo recognition data
- Study license plate reader data
- Establish links, as well as crime patterns.
Bottom Line
While it’ll still take a lot of legwork to solve a crime, robust, feature-rich investigation management software that draws conclusions, serves up the right information and allows for quick and easy analytics will make it that much easier to connect the dots, no matter the complexity of the situation.